|
|
Welcome to the World of Pulitzer Prize Winning Political Cartoonist Michael P. Ramirez |
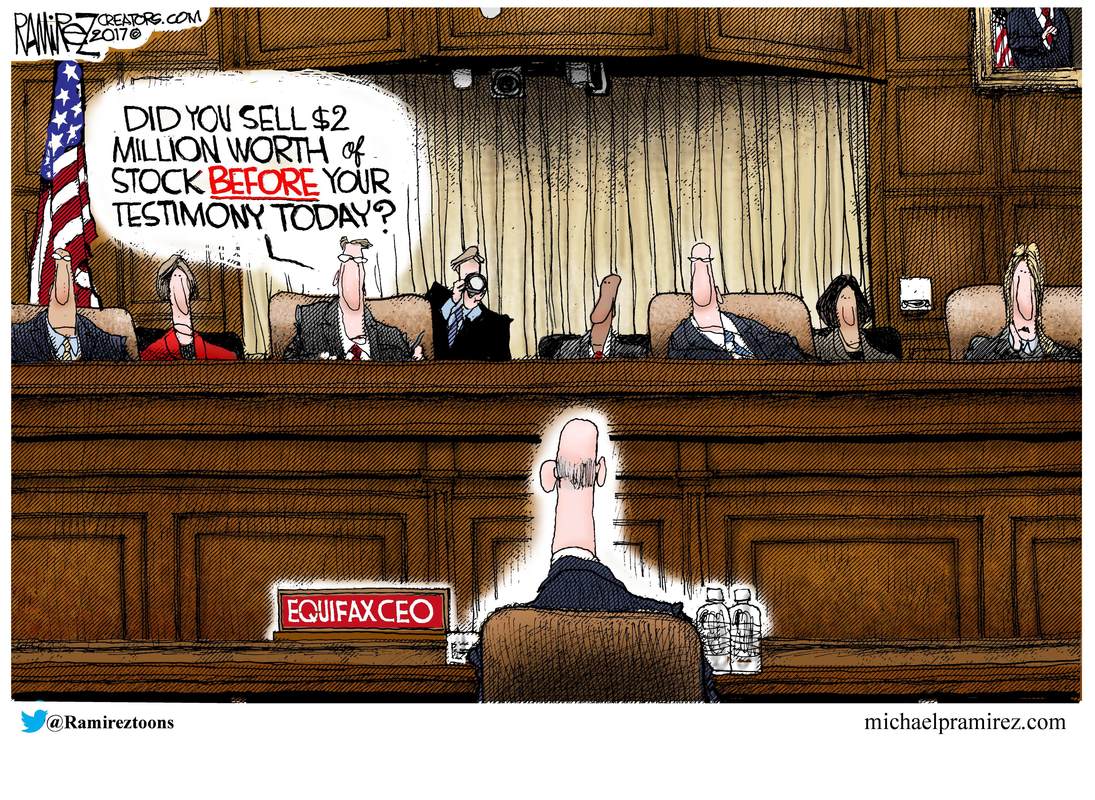
Equifax Stock Deal.... 10-07-17 See Michael's latest cartoons HERE
What We Learned from the Congressional Equifax Hearings This Week
by Jocelyn Baird October 6, 2017 NEXT ADVISOR
Nearly a month has passed since the massive breach of credit reporting bureau Equifax’s systems was revealed. According to a final report from the investigation released earlier this week, the breach comprised 145.5 million consumers’ details, including social security numbers. Immediately, the company was inundated with phone calls, website visitors and enrage. Three top-ranking officials, including Richard Smith, the company’s CEO, retired from their positions immediately in the aftermath, and calls for federal action were soon to follow. Congress requested that Smith come testify before a series of committees to discuss what went wrong, why the breach happened and what should be done about it. Join us as we break down the most important information learned in the Equifax hearings this past week and what it means for U.S. consumers going forward.
How many Equifax hearings were there?In total, over the course of three days — Oct. 3 to 5 — former Equifax CEO Richard Smith appeared before four different congressional committees to answer questions and give testimony. These committees were the House Committee on Energy and Commerce, the House Financial Services Committee, the Senate Banking Committee and the Senate Judiciary Committee. Representatives on both sides of the aisle were present at all four hearings, and they did not spare Smith their wrath, readily voicing disgust and anger that such a disastrous breach was able to happen — as well as lambasting Equifax’s poor attempts at responding and resolving the matter. Choice comments included calling the company’s response “sloppy” and quips such as, “I don’t think we can pass a law that fixes stupid.” Although many questions remain unanswered, there were definitely some important insights gleaned from these hearings.
What did we learn from the former CEO’s testimony?Here are the biggest takeaways from Richard Smith’s three days of testimony in Washington D.C.
1. The breach is being blamed on a single employee and failed technology. According to Smith, the breach was the result of a single employee on Equifax’s 225-person IT team who failed to communicate the need to perform a patch to one of Equifax’s “portals” after receiving an alert about the vulnerability and its available patch. If you remember from our previous post on this subject, the Apache struts vulnerability was discovered and patched within a day in early March 2017. In addition to this unnamed employee’s failure to do their job, Smith said that there was also a technological error when Equifax’s scanning software did not flag the unpatched system. Equifax is still investigating why the scanning system failed to pick up on the critical vulnerability, as it wasn’t until a “suspicious movement of data” occurred within the dispute portal that the breach was first discovered on July 29. While it’s easy to lay the blame on a single employee, it does lead one to wonder why it took four months for anyone to notice that such a dangerous vulnerability had never been patched. Only after the intrusion was discovered on July 29, according to Smith’s testimony, did the hole in the system get plugged.
2. Poor data security has been a long-term problem at Equifax. It’s clear from Smith’s testimony that the problems at Equifax expand far beyond one person dropping the ball and malfunctioning technology. Members of congress criticized the internal reporting structure at Equifax, citing the fact that the chief security officer reported the data breach to the chief legal officer instead of the CEO as unusual. Smith did not learn of it until July 31 — and the company did not contact the FBI until Aug. 2. It wasn’t until Aug. 15 that Smith became aware that consumer information was likely stolen. He defended himself and Equifax, stating that the company had spent $250 million in the past three years on data security, and noting that there was almost zero focus on cybersecurity when he took the helm in 2005.
However, this defense seems suspect when contrasted with the fact that the data stolen in the breach was not encrypted — instead, it was stored in plain text, meaning anyone who stumbled on it would have no issue reading and understanding it. Furthermore, Smith admitted that not all of Equifax’s core systems were encrypted either. Some security experts have questioned why the information of nearly 60% of the U.S. adult population was stored in a dispute portal in the first place. Despite his attempts at minimizing Equifax’s data security problems, there is plenty of evidence that Equifax has been asleep at the wheel for a long time — just a year ago, index provider MSCI Inc. wrote in a report that the credit bureau was ill-prepared to deal with a security problem and rated it a zero on privacy and security.
3. Waiting to publicly disclose the breach was an internal strategy. Equifax has been roundly criticized for waiting over a month to disclose the data breach to the public, and this was brought up at each of the hearings. Although the breach was discovered at the end of July, it wasn’t until Aug. 17 that Smith was informed of its severity, and the company’s board members were filled in between Aug. 22 and 25. A public disclosure announcement was not released until Sept. 7. When pressed on why it took so long to disclose, Smith said that it was a strategy suggested by Mandiant, the cybersecurity firm hired to investigate the breach, as they wanted to be sure that Equifax’s systems were protected — announcing a breach typically results in a significant increase in cyberattacks on a company. Despite this, some congress members were concerned that an 8-K form was not filed with the Securities and Exchange Commission (SEC) once the severity of the breach was realized, which would have notified investors that an announcement was impending which could impact the stock they were buying and selling. Note that the SEC, among other regulatory bodies, is currently investigating three Equifax employees who sold $1.8 million shares of Equifax stock during the time period between the data breach discovery and its public announcement.
4. Equifax may stand to profit from this disaster. In the midst of these hearings, it was announced that Equifax was awarded a $7 million government contract to help the IRS prevent fraud during tax season. This incensed a number of policy-makers, who questioned why a company that just lost the data of 145.5 million consumers deserved to be in charge of any kind of fraud prevention. The cold, hard truth about the credit bureaus is that their customers are not consumers — which Smith himself pointed out — but banks and other companies, such as LifeLock, which do business with Equifax and its ilk. Senator Elizabeth Warren grilled Smith over the fact that, just this past August, after the breach was already known to him, Smith delivered several speeches which claimed that fraud is an opportunity for Equifax. Since it does business with so many different financial companies, and because traditionally fees are charged whenever consumers place or lift a security freeze on their credit reports, identity theft and fraud can be money-makers for the credit bureaus.
5. The entire credit reporting industry needs to change. A common thread throughout each of the four hearings was the need for change across the credit reporting industry as a whole. Members of the Senate Banking Committee attacked the industry’s business model, asking why consumers don’t have power over the data that’s collected on them, and stating that consumers need to have more control over the collection, use and protection of personal identifying information (PII) by both government and private-sector entities. As most of us are aware, the information that credit reporting agencies collect is used to determine much of consumers’ financial lives, from their ability to take out a loan or open a credit card to the success of their relationships and job prospects. While questions as to whether it’d be wise for consumers to be able to request that their data be deleted were shot down by Smith — a deleted credit history could cause more headaches for consumers than they might realize — it’s clear that changes do need to be made. Suggestions for change included requiring controls over PII similar to what currently exists for medical data, a restructuring of the system to make it opt-in instead of opt-out and more accountability for the companies involved overall. Prior to these hearings, there was already legislature being proposed which would bar credit bureaus from charging fees to place or remove a credit freeze.
It is unlikely these hearings are the end of this debacle, as investigations are ongoing within the FBI, Department of Justice and other entities. The whole truth will probably never be known, but hopefully the information gleaned from Smith’s testimony will spur lawmakers into action to press for new regulations and protections on consumer financial data. To continue following this story, bookmark our Equifax blog. Learn more about protecting your credit and identity by following our identity theft protection blog.
by Jocelyn Baird October 6, 2017 NEXT ADVISOR
Nearly a month has passed since the massive breach of credit reporting bureau Equifax’s systems was revealed. According to a final report from the investigation released earlier this week, the breach comprised 145.5 million consumers’ details, including social security numbers. Immediately, the company was inundated with phone calls, website visitors and enrage. Three top-ranking officials, including Richard Smith, the company’s CEO, retired from their positions immediately in the aftermath, and calls for federal action were soon to follow. Congress requested that Smith come testify before a series of committees to discuss what went wrong, why the breach happened and what should be done about it. Join us as we break down the most important information learned in the Equifax hearings this past week and what it means for U.S. consumers going forward.
How many Equifax hearings were there?In total, over the course of three days — Oct. 3 to 5 — former Equifax CEO Richard Smith appeared before four different congressional committees to answer questions and give testimony. These committees were the House Committee on Energy and Commerce, the House Financial Services Committee, the Senate Banking Committee and the Senate Judiciary Committee. Representatives on both sides of the aisle were present at all four hearings, and they did not spare Smith their wrath, readily voicing disgust and anger that such a disastrous breach was able to happen — as well as lambasting Equifax’s poor attempts at responding and resolving the matter. Choice comments included calling the company’s response “sloppy” and quips such as, “I don’t think we can pass a law that fixes stupid.” Although many questions remain unanswered, there were definitely some important insights gleaned from these hearings.
What did we learn from the former CEO’s testimony?Here are the biggest takeaways from Richard Smith’s three days of testimony in Washington D.C.
1. The breach is being blamed on a single employee and failed technology. According to Smith, the breach was the result of a single employee on Equifax’s 225-person IT team who failed to communicate the need to perform a patch to one of Equifax’s “portals” after receiving an alert about the vulnerability and its available patch. If you remember from our previous post on this subject, the Apache struts vulnerability was discovered and patched within a day in early March 2017. In addition to this unnamed employee’s failure to do their job, Smith said that there was also a technological error when Equifax’s scanning software did not flag the unpatched system. Equifax is still investigating why the scanning system failed to pick up on the critical vulnerability, as it wasn’t until a “suspicious movement of data” occurred within the dispute portal that the breach was first discovered on July 29. While it’s easy to lay the blame on a single employee, it does lead one to wonder why it took four months for anyone to notice that such a dangerous vulnerability had never been patched. Only after the intrusion was discovered on July 29, according to Smith’s testimony, did the hole in the system get plugged.
2. Poor data security has been a long-term problem at Equifax. It’s clear from Smith’s testimony that the problems at Equifax expand far beyond one person dropping the ball and malfunctioning technology. Members of congress criticized the internal reporting structure at Equifax, citing the fact that the chief security officer reported the data breach to the chief legal officer instead of the CEO as unusual. Smith did not learn of it until July 31 — and the company did not contact the FBI until Aug. 2. It wasn’t until Aug. 15 that Smith became aware that consumer information was likely stolen. He defended himself and Equifax, stating that the company had spent $250 million in the past three years on data security, and noting that there was almost zero focus on cybersecurity when he took the helm in 2005.
However, this defense seems suspect when contrasted with the fact that the data stolen in the breach was not encrypted — instead, it was stored in plain text, meaning anyone who stumbled on it would have no issue reading and understanding it. Furthermore, Smith admitted that not all of Equifax’s core systems were encrypted either. Some security experts have questioned why the information of nearly 60% of the U.S. adult population was stored in a dispute portal in the first place. Despite his attempts at minimizing Equifax’s data security problems, there is plenty of evidence that Equifax has been asleep at the wheel for a long time — just a year ago, index provider MSCI Inc. wrote in a report that the credit bureau was ill-prepared to deal with a security problem and rated it a zero on privacy and security.
3. Waiting to publicly disclose the breach was an internal strategy. Equifax has been roundly criticized for waiting over a month to disclose the data breach to the public, and this was brought up at each of the hearings. Although the breach was discovered at the end of July, it wasn’t until Aug. 17 that Smith was informed of its severity, and the company’s board members were filled in between Aug. 22 and 25. A public disclosure announcement was not released until Sept. 7. When pressed on why it took so long to disclose, Smith said that it was a strategy suggested by Mandiant, the cybersecurity firm hired to investigate the breach, as they wanted to be sure that Equifax’s systems were protected — announcing a breach typically results in a significant increase in cyberattacks on a company. Despite this, some congress members were concerned that an 8-K form was not filed with the Securities and Exchange Commission (SEC) once the severity of the breach was realized, which would have notified investors that an announcement was impending which could impact the stock they were buying and selling. Note that the SEC, among other regulatory bodies, is currently investigating three Equifax employees who sold $1.8 million shares of Equifax stock during the time period between the data breach discovery and its public announcement.
4. Equifax may stand to profit from this disaster. In the midst of these hearings, it was announced that Equifax was awarded a $7 million government contract to help the IRS prevent fraud during tax season. This incensed a number of policy-makers, who questioned why a company that just lost the data of 145.5 million consumers deserved to be in charge of any kind of fraud prevention. The cold, hard truth about the credit bureaus is that their customers are not consumers — which Smith himself pointed out — but banks and other companies, such as LifeLock, which do business with Equifax and its ilk. Senator Elizabeth Warren grilled Smith over the fact that, just this past August, after the breach was already known to him, Smith delivered several speeches which claimed that fraud is an opportunity for Equifax. Since it does business with so many different financial companies, and because traditionally fees are charged whenever consumers place or lift a security freeze on their credit reports, identity theft and fraud can be money-makers for the credit bureaus.
5. The entire credit reporting industry needs to change. A common thread throughout each of the four hearings was the need for change across the credit reporting industry as a whole. Members of the Senate Banking Committee attacked the industry’s business model, asking why consumers don’t have power over the data that’s collected on them, and stating that consumers need to have more control over the collection, use and protection of personal identifying information (PII) by both government and private-sector entities. As most of us are aware, the information that credit reporting agencies collect is used to determine much of consumers’ financial lives, from their ability to take out a loan or open a credit card to the success of their relationships and job prospects. While questions as to whether it’d be wise for consumers to be able to request that their data be deleted were shot down by Smith — a deleted credit history could cause more headaches for consumers than they might realize — it’s clear that changes do need to be made. Suggestions for change included requiring controls over PII similar to what currently exists for medical data, a restructuring of the system to make it opt-in instead of opt-out and more accountability for the companies involved overall. Prior to these hearings, there was already legislature being proposed which would bar credit bureaus from charging fees to place or remove a credit freeze.
It is unlikely these hearings are the end of this debacle, as investigations are ongoing within the FBI, Department of Justice and other entities. The whole truth will probably never be known, but hopefully the information gleaned from Smith’s testimony will spur lawmakers into action to press for new regulations and protections on consumer financial data. To continue following this story, bookmark our Equifax blog. Learn more about protecting your credit and identity by following our identity theft protection blog.